OpenVPN Split Tunnel on Synology Diskstation
Last Updated Oct 21, 2019
Purpose
Remote access to a home network supporting the choice of split/full tunnel.
Requirements
- Ease of deployment. Preferably 1-click.
- Support for macOS, iOS, and, secondarily Windows.
- Strong encryption; compression is a plus.
- User authentication; either by passkey or public key. In the case of a passkey, autoblock should be configured after a few failed attempts.
- Supported/commercial solution is a plus (as opposed to hacking one together and supporting it forever)
What’s available
The following equipment supports Remote access VPN:
Unifi USG gateway: Supports PPTP and L2TP with Radius. PPTP is not serious and L2TP clashes with Back to My Mac ports
Sophos XG firewall: Supports all sorts of IPSEC but can’t terminate VPN connections in the bridge mode, until version 18.
VPN Server on Synology Diskstation: Supports PPTP, L2TP, and OpenVPN, with various user authentication options - Radius, LDAP, internal user base (which uses Radius as a backend anyway, as a plugin).
Proposal
OpenVPN seems like an obvious choice—the only downside being Synology can either be VPN Server or VPN Client but not both. This breaks a few useful scenarios such as mutual replication, but we’ll deal with this later.
Assumptions
We will make the following assumptions:
LAN: 10.0.17.0/24, suffix - home.example.com
Another LAN: 10.0.16.0/24 (you might have one)
Yet more LAN: 192.168.100.0/24 (common cable modem address)
VPN: 10.0.22.0/24
DNS: 10.0.17.1
Synology: 10.0.17.130
FDQN: home.example.com
User1: greg; [email protected]
User2: emili; [email protected]
IPv6: We don't bother for now
Configuring Server
Setup OpenVPN Server
This is fairly straightforward—from the Package Manager install OpenVPN server.
Launch it; on the General settings select:
- Network Interface to bind to
- Account types. Supported are Local Users, LDAP, and Radius if configured.
- Configure AutoBlock
On the Privilege page select users.
On the OpenVPN page, configure the server. Sample configuration on the screenshot:
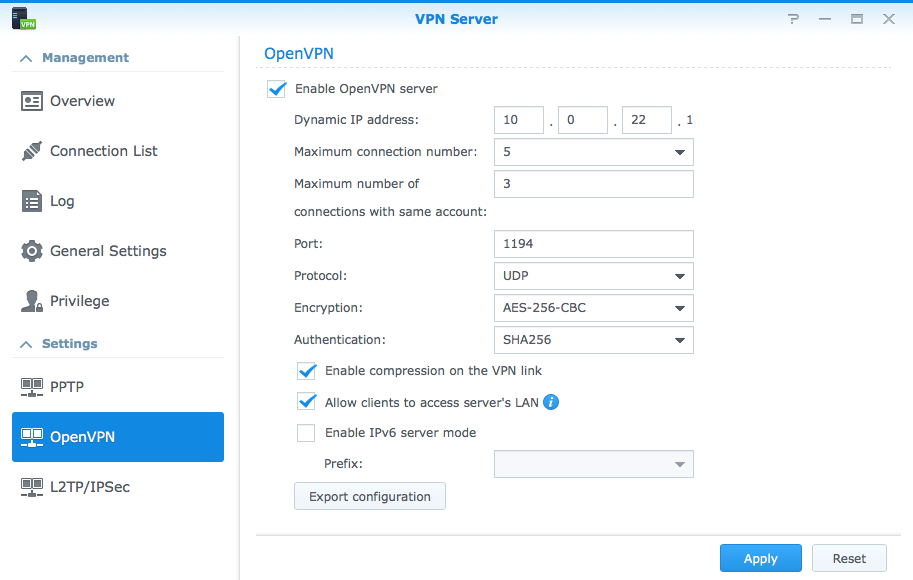
- Configure IP
- Port: leave at default,
1194 - Protocol:
UDPworks well - Encryption:
AES-256-CBCis recommended as secure and performant enough - Authentication:
SHA256shall do. - Enable Compression.
- Set “allow clients to access Server’s LAN”.
Export configuration.
Generate and edit .ovpn profiles
Now some trickery.
You will get four files
- VPNConfig.ovpn
- ca_bundle.crt
- ca.crt
- README.txt
Read through the VPNConfig.ovpn and make changes as directed below:
dev tun
tls-client
Add FDQN pointing to your external interface—likely on a gateway. It shall be configured to update via DDNS
remote home.example.com 1194
The float option is useful for mobile clients—I haven’t played with it much yet.
# The "float" tells OpenVPN to accept authenticated packets from any address,
# not only the address which was specified in the --remote option.
# This is useful when you are connecting to a peer that holds a dynamic address
# such as a dial-in user or DHCP client.
# (Please refer to the manual of OpenVPN for more information.)
#float
The next option redirect-gateway is important. You would want to make two copies of .ovpn profiles, one we will use for a split tunnel, in which redirect-gateway shall be commented out.
In the other one, for the full tunnel, leave it uncommented and add another line redirect-gateway ipv6. This is due to a requirement described here:
Note that iOS 7 and higher requires that if redirect-gateway is used, that it is used for both IPv4 and IPv6 as the above directive accomplishes.
The result for the full tunnel version of your file should look like this:
# If redirect-gateway is enabled, the client will redirect it's
# default network gateway through the VPN.
# It means the VPN connection will firstly connect to the VPN Server
# and then to the Internet.
# (Please refer to the manual of OpenVPN for more information.)
redirect-gateway def1
redirect-gateway ipv6
The dhcp-option DNS is configured automatically, but you would want to add the next two lines to facilitate split-tunnel functionality:
# dhcp-option DNS: To set primary domain name server address.
# Repeat this option to set secondary DNS server addresses.
dhcp-option DNS 10.0.17.1
dhcp-option DOMAIN home.example.com
dhcp-option DOMAIN-SEARCH home.example.com
Add additional static routes to reach other subnets if desired:
# Additional static routes
route 10.0.16.0 255.255.255.0 vpn_gateway
route 192.168.100.0 255.255.255.0 vpn_gateway
# Pull other configurations pushed from the server
pull
If your server has an SSL certificate (for example, obtained from Lets Encrypt automatically if using Synology DDNS, or commercially purchased certificate) you might want to turn on server certificate validation. It’s not much, it just requires that the server certificate was signed with explicit key usage and extended key usage based on RFC3280 TLS rules, in other words, to ensure that you are connecting to a designated server. No reason not to enable it really
remote-cert-tls server
Next, I would comment out script-security statement - we don’t need that, and this will avoid warnings in the clients. I would also add auth-nocache. Leave the rest of the options intact.
# If you want to connect by Server's IPv6 address, you should use
# "proto udp6" in UDP mode or "proto tcp6-client" in TCP mode
proto udp
#script-security 2
reneg-sec 0
auth-nocache
comp-lzo
cipher AES-256-CBC
auth SHA256
auth-user-pass
If you see references to certificate files—insert contents of ca_bundle.crt inline.
<ca>
-----BEGIN CERTIFICATE-----
...
-----END CERTIFICATE-----
-----BEGIN CERTIFICATE-----
...
-----END CERTIFICATE-----
</ca>
Now you should have full-tunnel.ovpn and split-tunnel.ovpn.
Configure DDNS and Firewall
On your gateway and/or firewall allow OpenVPN traffic from WAN to Synology box, and forward port 1194/udp.
Configuring Clients
Deploy both profiles, and select one or the other depending on whether the full or split tunnel is required.
macOS
Synology recommends Tunnelblick but I had some weird issues with it, and instead suggest using Viscosity (this is a non-affiliate link) for both macOS and Windows.
Install it and drop the.ovpn file onto it. That’s pretty much the end of it, nothing else needs to change—the defaults are sensible, and the rest of the configuration will be populated from the ovpn file.
You would need to configure the username and password, or you will be prompted when connecting, with an option to save it to the keychain. The rest should just work, including split-channel mode.
To confirm, on a Mac run scutil --dns – observe the sequence of dns suffix and resolvers in the very top.
So, does split-tunnel work? Well, let us try. I’m connected to corporate network corporate.com and started OpenVPN split-tunnel connection to home.example.com. chipmunk.home.example.com is another machine at home. hedgehog.corporate.com is a machine at the LAN.
$ ping chipmunk
PING chipmunk.home.example.com (10.0.17.12): 56 data bytes
^C
$ ping hedgehog
PING hedgehog.corporate.com (172.16.11.21): 56 data bytes
^
Ain’t that grate!
iOS
On iOS, it is just as easy:
- Install OpenVPN Connect
- Airdrop yourself .ovpn profile. It will open with OpenVPN app. Add the profile when prompted. This works most of the time; if it does not – email it to yourself, preferably not via the Internet, use local mail-server instead in the LAN. Opening the profile from the email never failed.
Note, you would need to initiate the connection from OpenVPN app; attempting to start VPN session from Settings → VPN will not work, at least when using user-auth-pass.
Does a split-tunnel work here as well? Yes. You can verify by pinging similar hosts via your favorite tool (such as Network Tools).
Windows
Haven’t tried it myself, but I’m pretty sure Viscosity would do just fine.
History
| January 1, 2018 | Initial publication |
| February 27, 2019 | Added static routes Added server certificate verification Fixed a few typos |
| October 21, 2019 | Added required ipv6 configuration for iOS devices to work in full tunnel mode |